sharing my simple wireguard kill-switch for Linux
cross-posted from: lemmings.world/post/8926396...
This magazine is from a federated server and may be incomplete. Browse more on the original instance.
cross-posted from: lemmings.world/post/8926396...
cross-posted from: lemmy.world/post/15187027...

Received notice of a change to the service in my inbox today. Seems icky to me....
Materialious now can be used as a Desktop or Android application. Allowing it to be used for any Invidious instance!...
Here’s what he said in a post on his telegram channel:...
(...

I used to use Protonmail, however the verification steps become tedious when creating unique emails for sign ups. I’ve switched to Tutanota despite it contravening their one account policy. What do you all use for one off emails (for sign ups etc )? Or do you prefer one of those 10 minute email sites?
I’ve attempted to create a VM on my ubuntu host machine that is accessing the internet via a dedicated VPN app. I’m able to disconnect my host VPN and access the web within the VM, but cannot access the web when the host VPN is enabled. Ideally I’d like to enable the VPN on the host and pass through web access to the VM....
12ft ladder doesnt seem to work anymore, on major sites at least. Does anyone have an alternative? Gracias
I use Aegis as my 2fa. Today on new token creation I observed that there’s hash function set to SHA-1, later checked all my tokens and the result is same type of encryption used for all. So I have edited all my tokens to SHA-256 as a result my totp doesn’t authenticate. Do I have to rescan my tokens for updating to SHA-256...
Virtual private networking (VPN) companies market their services as a way to prevent anyone from snooping on your Internet usage. But new research suggests this is a dangerous assumption when connecting to a VPN via an untrusted network, because attackers on the same network could force a target’s traffic off of the protection...

This post will be my personal experience about trying to gain back my privacy after years of being privacy unconscious. And foremost I want to apologize for my English, if it isn’t perfect, 'cause English is not my first language....
Pulling this off requires high privileges in the network, so if this is done by intruder you’re probably having a Really Bad Day anyway, but might be good to know if you’re connecting to untrusted networks (public wifi etc). For now, if you need to be sure, either tether to Android - since the Android stack doesn’t...

Hi, I used to use Instander to browse Instagram privately but it doesn’t seem to be updated anymore, is there an alternative that you recommend that has similar features? Like “ghost mode” when watching stories
Over the years I have saved many bookmarks in Firefox in various folders for interesting, useful or just frequently used websites....

Title is editorialized because the original is, frankly, clickbait garbage

I’m getting tired of the extremely loud ads on that don’t seem to be subject to the old TV broadcasting laws that prevent them from being blasted 10db louder than the actual content. Wondering if there’s stuff out there that would let me take the hdmi stream from my Apple TV or other streaming source, and do ad detection...
I remember there being apps like xender, easy share etc. which lets you share files by one person activating hotspot and the other wifi you just have to have both party close to each other and they use no data . But they are all closed source and probably spyware and its too much of a hassle to get others to download a file...
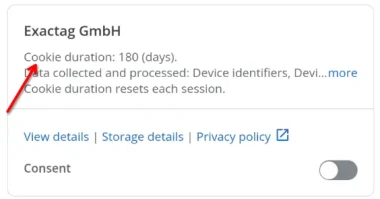
Yo peeps, I’m currently looking into TCF Vendors, Ad partners and their whole corporate greed hellhole of tracking. I am writing a paper on this, and would like for everything to be factually correct. However, I am struggling to understand one particular part of this “transparency framework” and hope someone can help me...
Simple steps to take before hitting the streets

Like it or not, email is a critical part of our digital lives. It’s how we sign up for accounts, get notifications, and communicate with a wide range of entities online. Critics of email rightfully point out that email suffers from a significant number of flaws that make it less than ideal, but that doesn’t change the...
