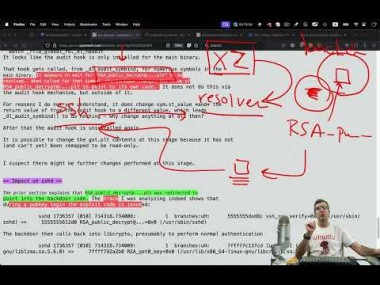
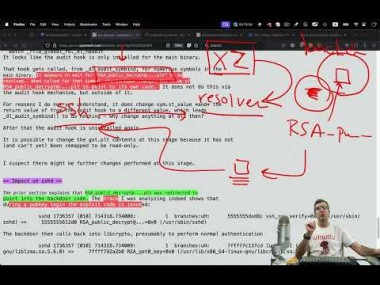
Unveiling the xz Utils Backdoor which deliberately opens our SSH connections for RCAs
mudle, 
For all those wanting to know what version of the xz package you have, DO NOT use
xz -Vorxz --version. Ask your package manager instead; e.g.apt info xz-utils. Executing a potentially malicious binary IS NOT a good idea, so ask your package manager instead.
j4yt33, I need the IASIP meme for this thumbnail
possiblylinux127, That thumbnail is something else
youngGoku, (edited ) So if I have been using arch with infected xz library to connect to a Debian LTS server, am I compromised?
cybersandwich, Assume yes until you can prove otherwise.
TwiddleTwaddle, From what I’ve read both arch and debian stable aren’t vulnerable to this. It targeted mostly debian-testing.
rotopenguin, 
As I heard it - the (naughty) build tooling looked for rpm and deb, and bailed out if they were absent.
Irate1013, Arch put out a statement saying users should update to a non infected binary even though it doesn’t appear to affect Arch archlinux.org/…/the-xz-package-has-been-backdoore…
However, out of an abundance of caution, we advise users to remove the malicious code from their system by upgrading either way. This is because other yet-to-be discovered methods to exploit the backdoor could exist.
possiblylinux127, I would pay attention to the news. You definitely want to upgrade immediately if you have not already
perishthethought, Good explainer, if you need to catch up like I did:
en.m.wikipedia.org/wiki/XZ_Utils
Read the supply chain attack section.
Also, from the video…
X is losing its action! We LIKE!
Hell yeah we like.
tsonfeir, 
Anyone got a link for this topic that isn’t a video?
BOFH666, Check the links on that page.
BOFH666, Thanks for the pointer.
This is really huge, but people don’t quite understand that yet.
If this wasn’t caught, every system -running public sshd- could be hacked or abused/misused.
And I completely agree with the last words, corporate should pay foss projects!
SMillerNL, Even paid it might be hard to find maintainers with knowledge of the code
p03locke, 
Add comment